Convert YouTube videos to MP4 quickly and for free with no loss in quality using the best YouTube to MP4 Converter!
Paste the URL of the YouTube video you'd like to convert to MP4. Note that only videos set to public and downloadable can be converted.
Click 'Download' and wait just a few moments for AI Studios to convert it into a downloadable MP4 video file.
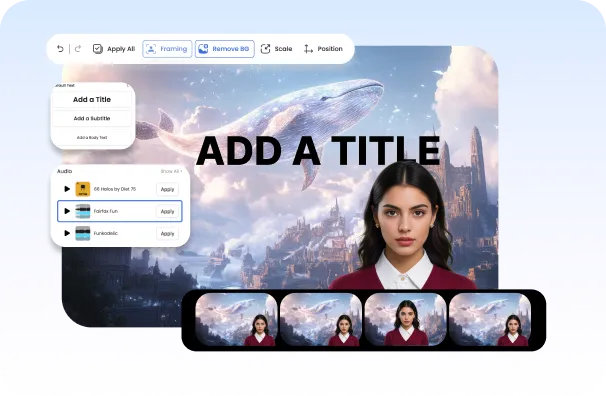
You have the option to edit your video using AI Studios’ built-in video editor or click “Download” to save your video to your device.

AI Studios’ YouTube to MP4 converter is entirely web-based, allowing you to convert videos from any browser, anywhere in the world. There's no need to download bulky software to your computer! Just convert your YT to MP4 online for free.

AI Studios' YT to MP4 converter is a convenient tool that simplifies the process of downloading and converting YouTube videos. With our user-friendly interface and straightforward setup, it’s designed to be accessible even for those without any video editing experience.

Ideal for content creators, our YouTube to MP4 Downloader streamlines the process of repurposing videos for platforms like TikTok, Instagram, and more. Utilize AI Studio’s advanced YouTube editing tools to transform your converted YouTube MP4 files into fresh content or adapt them for different platforms.
This content is for educational and informational purposes only. The author does not condone bypassing security locks on devices you do not own.
Note: This term is often used in contexts like bypassing activation locks on mobile devices (iOS/Android), creating temporary high-speed environments for manufacturing, or forensic bypasses. The following post assumes the technical/security research context (e.g., iOS ramdisk booting for legacy activation), but it is framed as an educational cybersecurity piece. In the world of low-level system recovery, jailbreaking, and embedded systems forensics, few techniques sound as clandestine or powerful as Ramdisk Factory Activation . It sounds like something out of a cyberpunk novel—booting a device into a phantom state where security checks are neutered, and the system believes it has just left the assembly line.
However, for vintage device collectors, data recovery specialists, and reverse engineers studying legacy hardware, the ramdisk method remains a fascinating artifact of mobile security history. Ramdisk Factory Activation represents the eternal cat-and-mouse game between device security and those who wish to bypass it. It is a powerful, low-level hack that gives the operator root access before the operating system even knows it's running.
refers to the process of tricking a device (typically an iPhone, iPad, or Android device) into booting from a custom, minimal operating system loaded entirely into that RAM, rather than from its onboard flash storage.
With great power comes great responsibility. Only perform these techniques on devices you own legally, or in a controlled lab environment for educational research. Have you ever attempted to recover a legacy device using a custom ramdisk? Share your experiences (and warnings) in the comments below.
But what is it actually? And why do security researchers, data recovery specialists, and legacy device collectors covet this method? At its core, a Ramdisk is a block of your system’s RAM (Random Access Memory) that is partitioned and formatted to act like a disk drive. Unlike a hard drive or SSD, RAM is volatile —it loses all data when power is cut.
Sign up for a free AI Studios demo & experience all
the best of AI content creation in one platform.